On-Chain Asset Security in the AI Era: A Practical Guide from Private Key Protection to DeFi Risk Control (2026 Edition)
Why On-Chain Security Strategies Must Be Rewritten for 2026
If you’re still using the 2021 approach of “just back up your seed phrase,” your risk management is already behind the curve. On-chain security now faces three major shifts:
- Attacks have moved from “breaking cryptography” to “manipulating human decision-making.”
- Losses have shifted from “private key theft” to “users willingly signing dangerous approvals.”
- Risks have escalated from “lone hackers” to “industrialized black market tools and AI-driven automation” working together.
This means that for retail investors, the focus must move from “protecting secrets” to “managing every single interaction.”
What Recent Developments Show: Risks Have Shifted from “Hacker Skills” to “Human-AI Collaborative Scams”
Recent public data from the past two years highlights several key trends:
-
Major incidents still occur: The 2025 Bybit incident, tracked by multiple agencies, is a historic loss case that exposed weaknesses in third-party dependencies, signature workflows, and supply chain security. The takeaway for everyday users: you don’t need to be “hacked”—one signature on the wrong interface can lead to irreversible loss.
-
AI-powered scams are on the rise: Multiple 2026 industry reports show that impersonated customer support, voice cloning, deepfake videos, and mass phishing are rapidly expanding. Scammers no longer rely on “obvious typos,” but on convincing communication, emotional manipulation, and urgency—getting you to make mistakes within just 3 minutes.
-
Regulation is raising standards, but won’t cover your losses: Hong Kong’s stablecoin licensing and the implementation of Europe’s MiCA have improved institutional compliance and transparency. However, regulation mainly reduces “systemic opacity” and cannot stop individuals from signing malicious Permit or SetApprovalForAll transactions on phishing sites.
Bottom line: While the external environment is improving, user-side operational risk remains the leading cause of loss.
Building a Security Foundation: Three-Tier Isolation for Private Keys, Devices, and Identity
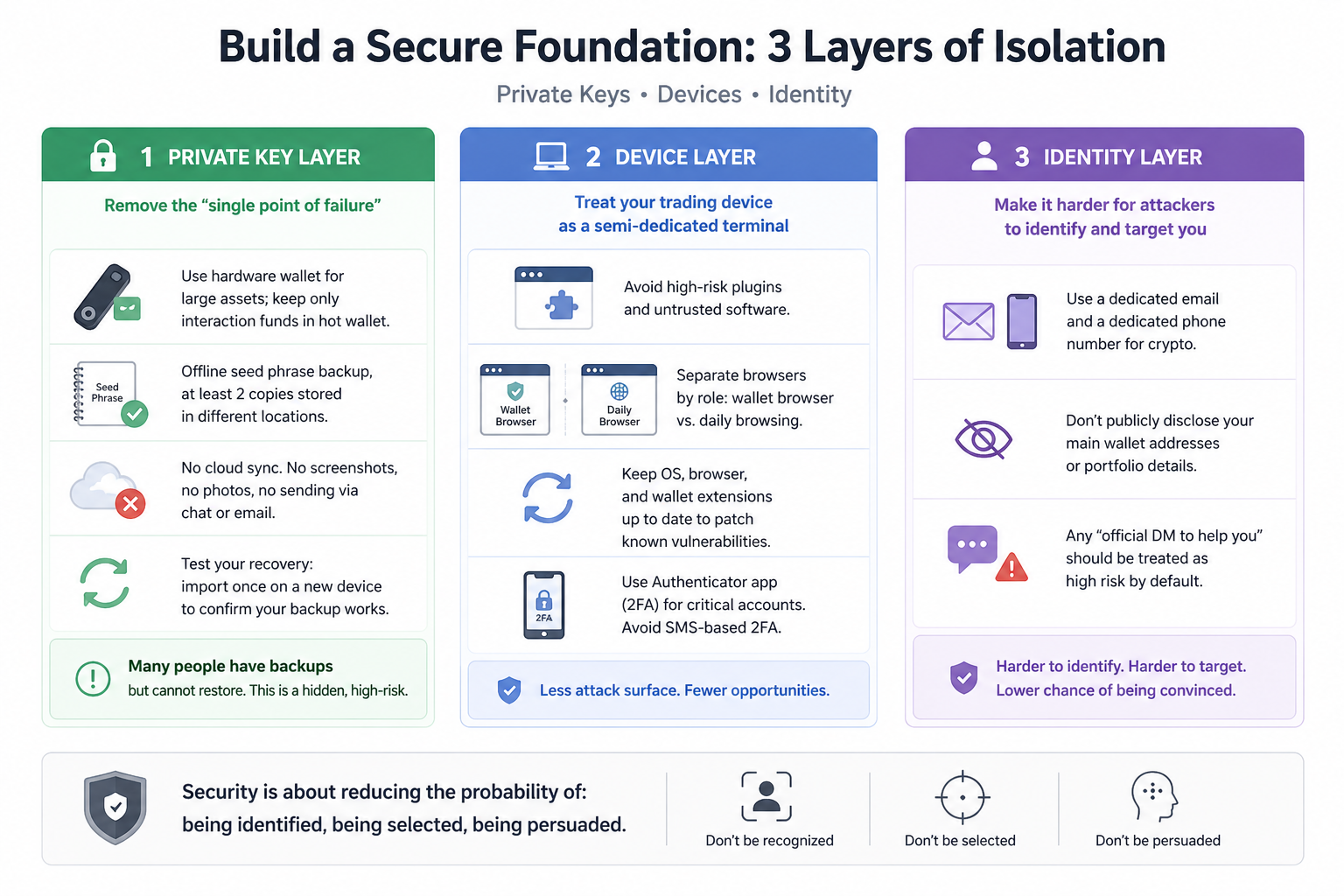
1. Private Key Layer: Eliminate Single Points of Failure
- Store large Assets in Hardware Wallets; keep only transaction funds in Hot Wallets.
- Back up your seed phrase offline, in at least two separate locations.
- Never enable cloud sync, take screenshots, photos, or share via chat apps.
- Practice recovery: import your backup on a new device to confirm it works.
Many users “have a backup but can’t restore”—a hidden high-risk scenario.
2. Device Layer: Treat Trading Devices as Semi-Dedicated Terminals
- Avoid installing high-risk plugins or unknown software on your main trading device.
- Use browser isolation: separate your main Wallet browser from your everyday browser.
- Keep your OS, browser, and Wallet extensions updated to patch vulnerabilities.
- Use Authenticator-based 2FA for key accounts; avoid SMS verification.
3. Identity Layer: Make It Difficult for Scammers to Target You
- Use a dedicated Email and phone number for crypto Assets.
- Never disclose your main Wallet Address or holdings on social media.
- Treat any “official private assistance” as high risk by default.
Security is about lowering the chances of being identified, targeted, or persuaded.
The Heart of DeFi Security: Are You Earning Return or Selling Risk Exposure?
DeFi risk isn’t abstract—it’s a set of tangible, measurable exposures. Use this framework for decision-making:
1. The 5 Essential Protocol Due Diligence Checks (Reduce Allocation If Any Are Missing)
- Is the contract open source and audited?
- What is its uptime and incident history—any pauses or rollbacks?
- Is TVL and liquidity structure healthy, or highly concentrated?
- Are management permissions upgradable, and who controls upgrades?
- Have the oracle and liquidation mechanisms been stress-tested?
2. Approval Management: More Critical Than Token Selection
- Reject default Unlimited Approval.
- For new protocols, start small: short approvals, single-Asset tests.
- Clean up approvals monthly.
- Be extra cautious with SetApprovalForAll in NFT scenarios.
Remember: attackers often target forgotten approvals, not just your Private Key.
3. Position Structure: Minimize Total Loss Probability
Adopt a three-tier fund allocation:
- Core Position (60%–80%): Cold storage or low-interaction Assets.
- Strategy Position (20%–35%): Robust strategies in mature protocols.
- Experimental Position (5%–10%): New protocols, chains, or narratives.
Even if the experimental position is lost, your Principal remains secure.
New AI-Era Attack Surfaces: Deepfakes, Customer Support Impersonation, and Automated Phishing
Today’s biggest risk isn’t “hackers in the code,” but “scammers in the chat.” Build anti-social engineering routines—don’t rely on gut instinct.
High-risk warning signs:
- Someone demands immediate action and creates a countdown.
- Claims of “account anomalies” requiring your seed phrase or Private Key.
- Signature requests where you don’t understand the permission changes.
- Links sent via social media DMs, group bots, or unfamiliar short links.
- Offers of “approve first, refund later” or “sign first, unfreeze later.”
Countermeasures (always execute):
- Only access official sites via bookmarks—never click DM links.
- Pause for 10 min after any anomaly; double-check domains and contract addresses.
- For approvals, set Wallet to precise amounts and short-term permissions only.
- For large transactions, use a test Wallet to run through the process first.
Procedural discipline beats emotional reactions—your best defense against AI-driven scams.
30-Day Security Upgrade Plan for Everyday Users
Don’t try to do everything at once—spread improvements over four weeks.
Week 1: Lay the Foundation
- Create Cold, Hot, and test Wallets.
- Complete two offline seed phrase backups.
- Enable 2FA for Email, trading platforms, and social media.
Week 2: Eliminate Existing Risks
- Review all approvals and revoke unused permissions.
- Move large Assets to low-activity addresses.
- Whitelist bookmarks for trusted sites.
Week 3: Strengthen Processes
- Set a “double confirmation for large transfers” rule: address, network, and amount.
- For new protocols, always “test small -> review -> scale up.”
- Set alerts for key Assets and liquidation prices.
Week 4: Run Drills
- Practice Wallet recovery.
- Simulate a phishing emergency.
- Review and update your personal SOP.
Security is not a one-time setup—it’s a repeatable habit system.
The Critical 60 Minutes After an Incident: Emergency SOP
If you suspect you’ve signed a suspicious transaction, follow these steps—without hesitation:
- Isolate: Disconnect from suspicious sites; stop all signing.
- Transfer: Move unaffected Assets to a new address immediately.
- Revoke: Clean up high-risk contract approvals right away.
- Record: Save transaction hash, time, address, and screenshots.
- Review: Identify if it was a phishing Link, malicious extension, or social engineering.
Many losses are amplified not by the first signature, but by a series of panicked mistakes.
Final Thoughts: Make Security Part of Your Long-Term Return
In the AI era, on-chain Asset security isn’t just for tech experts—it’s a core survival skill for everyone. What you need isn’t more “insider tips,” but fewer mistakes, clearer permission boundaries, and stronger execution discipline.
Follow this principle:
Protect your capital first, then seek growth; prioritize process, then pursue Return.
When you institutionalize Private Key management, approval governance, protocol due diligence, and emergency response, the volatility of the on-chain world doesn’t just mean high risk—it can become your long-term edge.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

Sui: How are users leveraging its speed, security, & scalability?
Dive into Hyperliquid
What Is a Yield Aggregator?

What is Stablecoin?


