What are Monero's Ring Signatures? How does XMR conceal the sender in a trade
As on-chain analysis tools evolve, the traceability of public blockchains continues to intensify. While Bitcoin addresses are not directly tied to real-world identities, transaction paths, address clustering, and KYC data associations now enable user behavior to be identified to a certain degree.
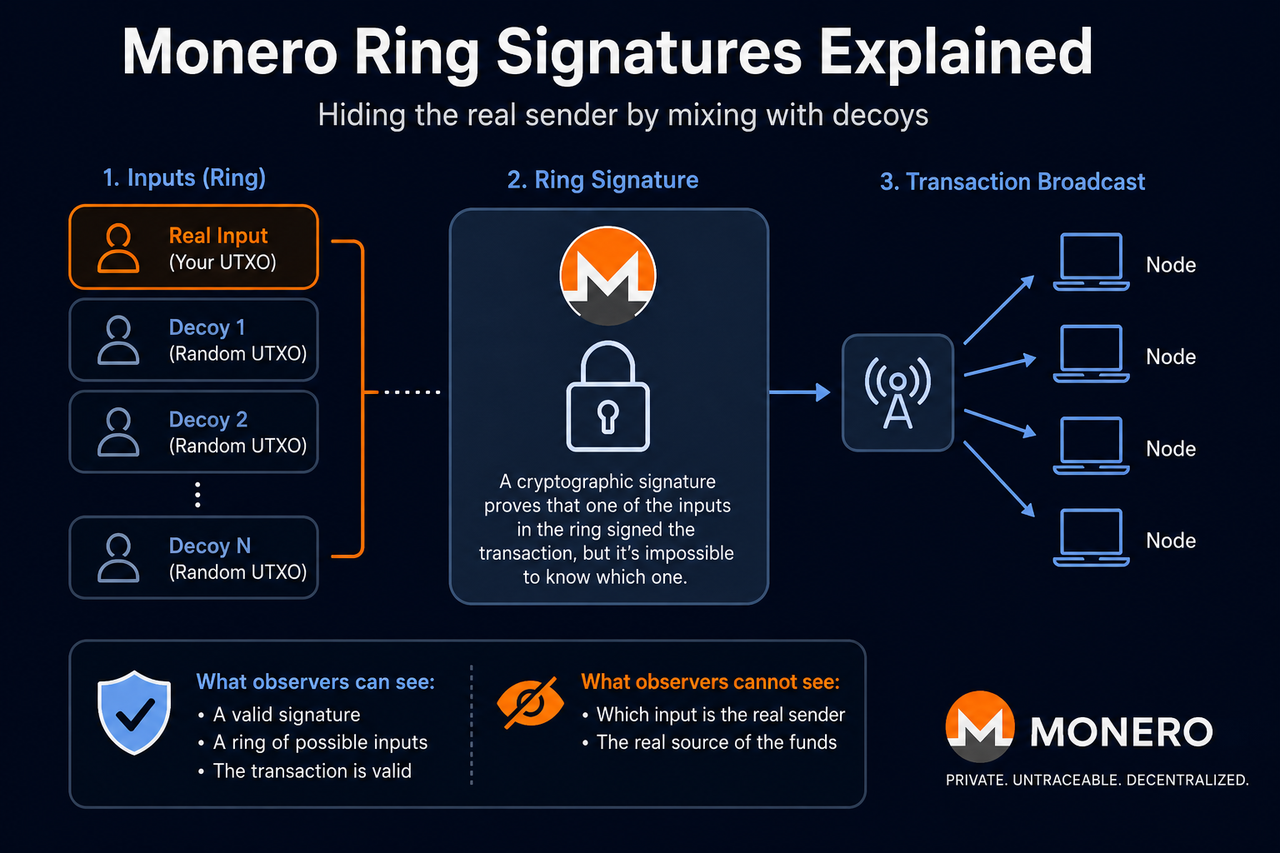
Ring Signatures serve as one of the most critical anonymity mechanisms in the privacy-centric cryptocurrency Monero. Unlike transparent public blockchains, Monero conceals the true sender of a transaction by blending the actual input with multiple historical outputs, preventing external observers from pinpointing the fund source.
What Are Ring Signatures?
Ring Signatures are a cryptographic signature method designed to obscure the identity of the actual signer. In the Monero network, when a user initiates a transaction, the system does not sign solely with the real input—instead, it randomly selects several historical outputs from the blockchain, combining them with the actual input to form a “ring.”
Validators can verify that the transaction was initiated by one of the ring members and that the signature is valid, but they cannot determine which participant is the true sender. This architecture makes it extremely challenging to directly trace Monero transaction sources.
Unlike conventional digital signatures, ring signatures do not require the real signer’s identity to be revealed, instead emphasizing “group anonymity.” Consequently, Monero’s privacy does not stem from hiding the transaction’s existence, but rather from masking the true source of the input.
Why Does Monero Hide Transaction Senders?
A core attribute of public blockchains is transparency. For example, in Bitcoin, all transaction inputs and outputs are permanently recorded on-chain, allowing anyone to view fund flows, address balances, and transaction histories.
While addresses are typically strings, on-chain analytics firms can build user profiles by linking addresses, analyzing transaction patterns, and mapping fund flows. If users are associated with exchange KYC data, the traceability of public ledgers becomes even more robust.
Monero seeks to minimize this analyzability, introducing Ring Signatures to obfuscate transaction sources. By hiding the actual input, Monero reduces the accuracy of address clustering and fund tracing, thereby enhancing user privacy.
How Do Ring Signatures Work?
When a user initiates a Monero transaction, the wallet first selects a real available output as the transaction input. The system then randomly picks several other outputs from blockchain history as decoys, forming a signature ring with the real input.
The wallet generates a unified signature for the entire input set. To external observers, it is clear that the transaction originated from one of the ring members, but it is impossible to determine which input is genuine.
Once the transaction is broadcast, nodes validate the signature and ensure no double-spending occurs, but do not reveal the real source of funds. Unlike Bitcoin, where fund flows are fully transparent, Monero’s transaction inputs are concealed within an anonymity set.
What Is an Anonymity Set?
An anonymity set refers to all possible candidates in a transaction that could serve as the true sender.
For instance, if a ring contains 16 outputs, external observers know only that the real input is among those 16, but cannot identify which one. Theoretically, the larger the anonymity set, the harder it is to perform on-chain analysis—and the stronger the transaction privacy.
Monero has consistently increased the default ring size to strengthen overall anonymity. Since ring signatures are mandatory for all transactions, the network shares a large anonymity pool, rather than relying on a handful of private transactions for localized privacy.
How Does Key Image Prevent Double-Spending?
Although Ring Signatures conceal the real input, the network must still prevent double-spending.
Monero addresses this with the Key Image mechanism. Each real output generates a unique Key Image when spent, which does not reveal the real address, but allows the network to check if it has already been used.
If a Key Image appears more than once, the associated funds have already been spent and the transaction is rejected. This design enables Monero to prevent double-spending without exposing the real input.
How Does the CLSAG Upgrade Improve Ring Signatures?
Monero initially used the MLSAG (Multilayered Linkable Spontaneous Anonymous Group) structure for ring signatures.
The network later upgraded to CLSAG (Concise Linkable Spontaneous Anonymous Group) to boost verification efficiency and reduce transaction data size.
CLSAG’s main advantages include smaller transaction size, faster verification, and lower trading fees. For Monero, this upgrade improved on-chain performance and scalability while maintaining privacy.
How Do Ring Signatures Differ from the Bitcoin UTXO Model?
Both Monero and Bitcoin operate on the UTXO model, but their privacy approaches differ significantly.
| Comparison Dimension | Monero Ring Signatures | Bitcoin UTXO |
|---|---|---|
| Input Source | Hidden by default | Fully public |
| Transaction Tracking | Highly difficult | Directly analyzable |
| Address Clustering | Difficult to cluster | Easy to cluster |
| Default Privacy | Yes | No |
| On-Chain Transparency | Low | High |
Bitcoin prioritizes openness, transparency, and verifiability, whereas Monero prioritizes transaction anonymity and privacy.
Are Ring Signatures Fully Anonymous?
Ring Signatures make on-chain tracking more difficult, but do not guarantee “absolute untraceability.”
Privacy can be affected by factors such as decoy selection quality, user transaction habits, network-level data leaks, and external KYC data. Early versions of Monero with smaller default ring sizes also offered weaker anonymity.
Thus, Monero’s goal is not absolute anonymity, but to enhance privacy by raising the cost of on-chain analysis.
Summary
Ring Signatures are a core technology in Monero (XMR)’s privacy framework, primarily used to hide the real transaction sender’s identity. By blending real inputs with multiple historical outputs, Monero creates an anonymity set, reducing the effectiveness of address clustering and fund tracing.
Meanwhile, the Key Image mechanism prevents double-spending without disclosing the real input, and the CLSAG upgrade further optimizes transaction efficiency and network performance.
FAQs
Why Does Monero Use Ring Signatures?
Monero uses Ring Signatures to minimize transaction traceability and prevent on-chain analysis tools from directly identifying fund sources.
What Is an Anonymity Set?
An anonymity set is the group of possible candidate outputs in a ring that could be the real sender. The larger the set, the stronger the privacy.
How Do Ring Signatures Prevent Double-Spending?
Monero utilizes the Key Image mechanism to detect and block double-spending, safeguarding privacy while ensuring funds cannot be spent twice.
What Is CLSAG?
CLSAG is Monero’s upgraded ring signature protocol, reducing transaction size, increasing verification efficiency, and lowering trading fees.
Are Ring Signatures Fully Anonymous?
No. While Ring Signatures make tracking transactions more difficult, network activity, KYC data, and statistical methods can still impact privacy.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?