How Does Sign’s Decentralized Identity Mechanism Work? An Analysis of Its Operational Flow and Technical Architecture
Within the Web3 ecosystem, identity has long presented a structural challenge. Traditional blockchain addresses are decentralized, but they lack verifiable identity information, making it difficult to establish stable trust relationships across different applications. As DeFi, DAO governance, onchain social networks, and AI agents continue to expand, building a trustworthy identity framework while preserving privacy is becoming an essential component of Web3 infrastructure.
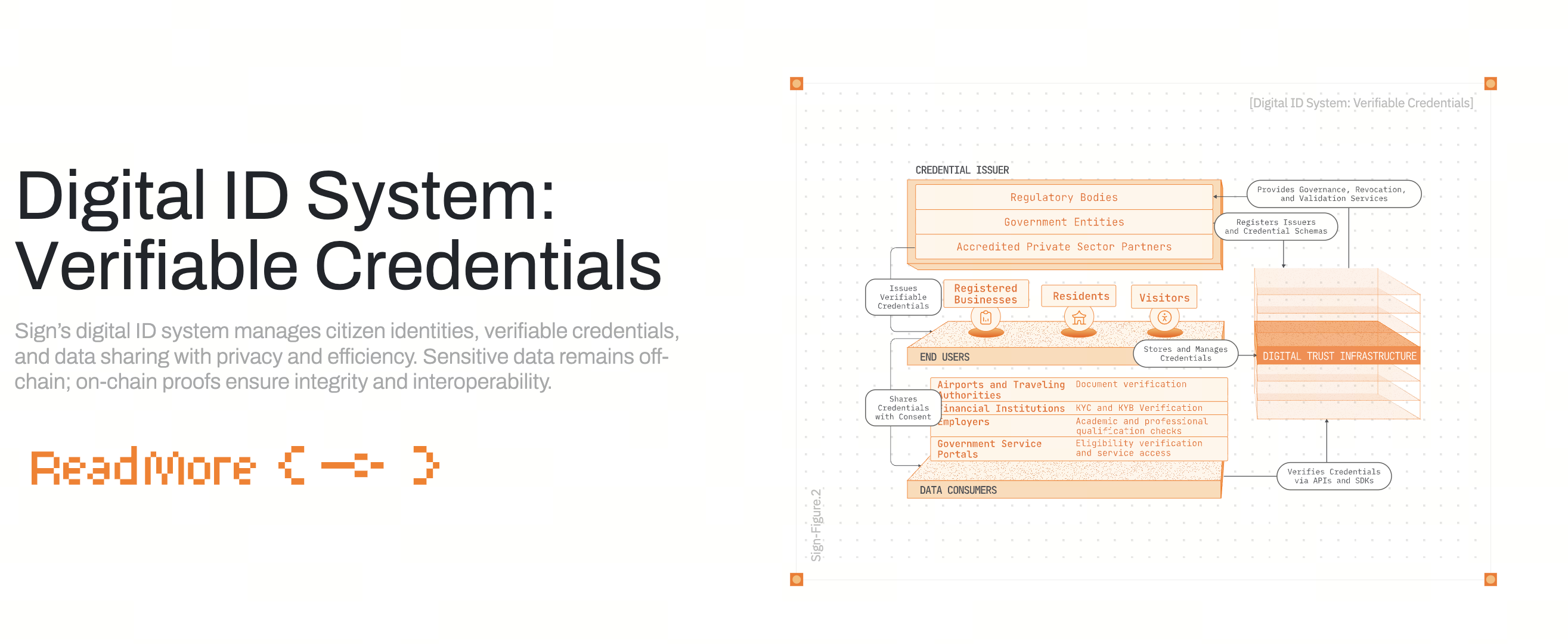
From a technical architecture perspective, Sign Protocol attempts to create a composable identity layer through its onchain attestation system. Identity is no longer controlled by centralized institutions. Instead, users, projects, and third party verification entities collectively participate in generating and validating identity data. Through cross chain compatibility, verifiable data structures, and privacy protection mechanisms, Sign aims to provide Web3 applications with a more open and reliable identity foundation.
Overview of Decentralized Identity Management (DID)
Decentralized Identity (DID), is an identity management framework that allows individuals to control their own identity information. Unlike traditional internet systems where platforms manage user identities, DID enables users to own and manage their identity data on the blockchain.
In traditional Web2 environments, user identity is typically stored and controlled by large platforms such as social media companies or internet service providers. This model creates several problems, including data silos, privacy leakage risks, and extensive platform control over user identity.
The core concept behind DID is Self Sovereign Identity (SSI), meaning users maintain full ownership and control over their personal identity. Instead of relying on a single institution, identity information is managed by the user through cryptographic keys and onchain data structures.
In the Web3 ecosystem, DID typically includes three key components:
-
Decentralized Identifiers (DID Identifier)
-
Verifiable Credentials
-
Verifiable Data Registries
Sign Protocol builds on this framework by connecting DID systems with blockchain applications through its attestation mechanism. As a result, identity data can be shared and verified across multiple protocols and platforms.
The Identity Attestation Generation Process in Sign Protocol
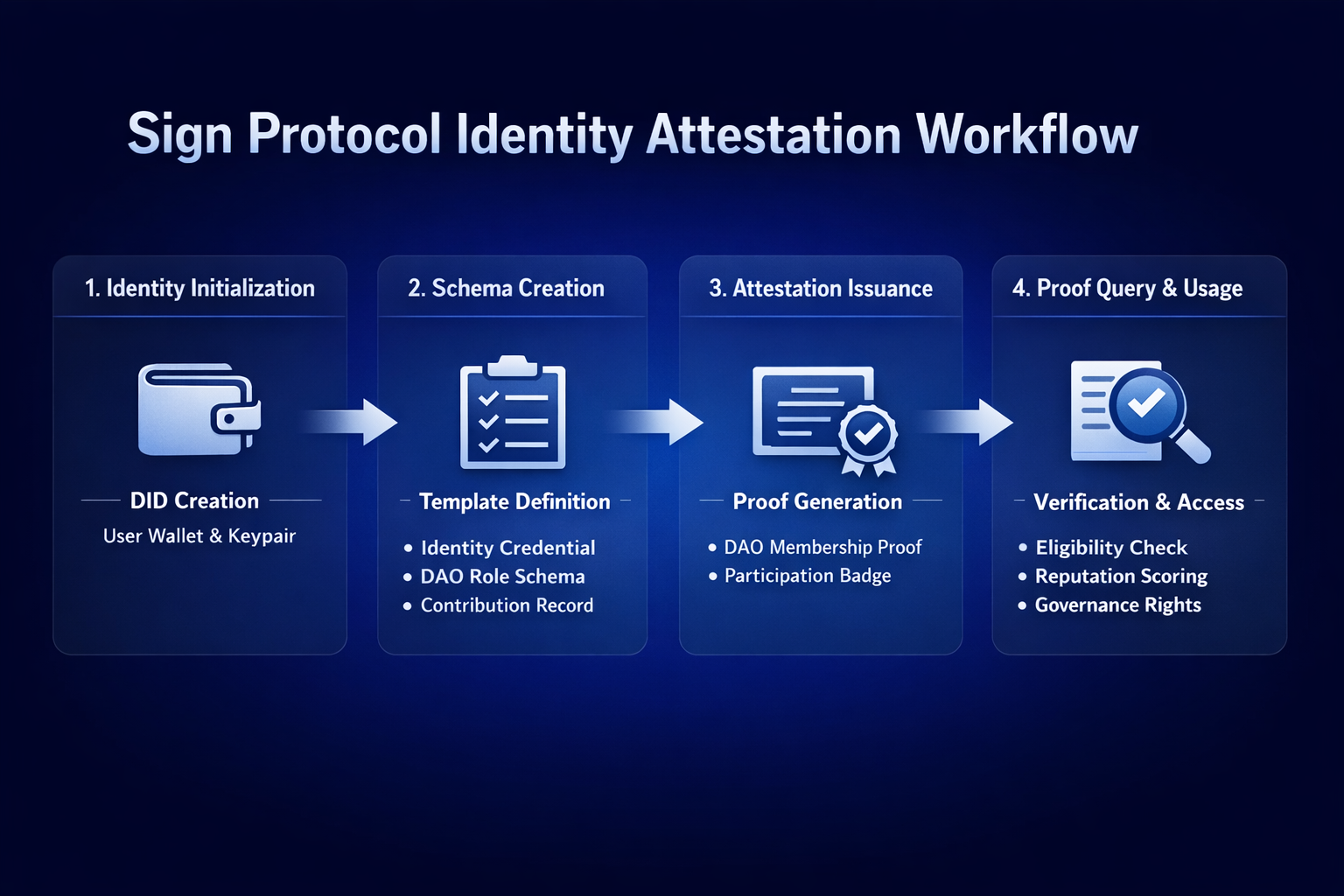
The core function of Sign Protocol is generating onchain attestations. These attestations can be understood as blockchain based credentials that record a claim made by one entity about another entity’s identity or behavior.
The identity generation process typically includes several key steps.
Step 1: Identity Initialization
Users first create a decentralized identity through their wallet address. Within the Sign system, the wallet address serves as the primary DID identifier, and the user controls this identity through their private key.
Step 2: Attestation Schema Creation
Projects or organizations can create attestation schemas. A schema defines the structure of the attestation data, for example:
-
Identity verification
-
DAO membership
-
Project contribution records
-
Onchain activity proof
Schemas ensure that attestation data follows a standardized format, allowing credentials to be reused across different applications.
Step 3: Attestation Issuance
When a user meets certain criteria, a verifier can issue an attestation to the user’s address. For example:
A DAO may issue contribution attestations to active contributors.
A project may issue participation credentials to early users.
These attestations may either be recorded directly onchain or stored offchain within verifiable data structures.
Step 4: Attestation Query and Usage
Other applications or protocols can query these attestation records to determine whether a user meets specific conditions, such as:
-
Whether the user is an early participant
-
Whether the user has a record of contributions
-
Whether the user has completed identity verification
Through this mechanism, Sign transforms identity and behavioral data into composable onchain assets.
Sign’s Multi Layer Verification Mechanisms and Security Model
To ensure the authenticity and security of attestation data, Sign Protocol implements multiple verification layers.
- Signature Verification
Each attestation must be cryptographically signed by the issuing party. Verifiers can confirm the authenticity of the data simply by validating the signature and checking the issuer’s address.
- Blockchain Immutability
Once attestations are recorded onchain, their data structure is protected by the blockchain’s consensus mechanism. Historical records cannot be arbitrarily modified.
- Verifiable Data Structures
Sign uses a structured schema system to standardize attestation formats. This approach helps prevent data forgery and ensures compatibility across different applications.
In addition, some attestations can integrate Zero Knowledge Proof technology. With ZK mechanisms, users can complete verification without revealing their full identity information.
For example, a user may prove that:
-
They belong to a certain country
-
They meet a particular credit score requirement
-
They hold membership in a DAO
All of this can be verified without exposing sensitive personal data. This significantly improves both security and privacy protection within the identity system.
Understanding the Logic of Cross Chain Identity Verification
As multi chain ecosystems expand, identity systems tied to a single blockchain can no longer meet the needs of Web3 applications. Sign Protocol therefore incorporates cross chain functionality into its architecture.
Cross chain identity verification typically involves three core components:
-
Identity Data Layer: Identity attestations may originate on a primary chain such as Ethereum, BNB Chain, or a Layer2 network.
-
Cross Chain Messaging Layer: Cross chain messaging protocols allow attestation data to be synchronized or referenced across different blockchains.
-
Verification Logic Layer: Applications on the destination chain can read, verify, and utilize attestation data.
For example, a user may obtain a DAO contribution attestation on Ethereum. A DeFi protocol on another blockchain can then read this credential and grant specific permissions or rewards.
This design gradually transforms onchain identity into a cross chain credential system that works across the broader Web3 ecosystem. As cross chain infrastructure continues to mature, the mobility of identity data between blockchains is likely to increase.
User Control and Privacy Protection in Sign Architecture
One of the core principles of Sign Protocol’s design is user control over identity data.
In traditional identity systems, users rarely have the ability to determine which data is shared or disclosed. Within the Sign ecosystem, however, users can decide which attestations are public and which remain private.
Privacy protection is typically achieved through several mechanisms:
-
Selective Disclosure: Users reveal only the necessary information. For example, proving DAO membership without exposing a complete activity history.
-
Offchain Storage with Onchain Verification: Sensitive data can be stored offchain, while the blockchain records only hashes or proof structures.
-
Zero Knowledge Proofs: Conditions can be verified without revealing the original data.
This architecture allows Sign to balance verifiable trust with strong privacy protection. For Web3 applications that require identity verification but must safeguard user privacy, this design offers significant advantages.
Sign’s Advantages and Innovations in Identity Management
Compared with traditional identity systems, Sign Protocol introduces several important innovations.
- Onchain Attestation Model
Sign converts identity verification into verifiable data structures, turning identity itself into a composable onchain resource.
- Open Verification Framework
Any project or organization can create attestation schemas on Sign, expanding the scope of identity verification and enabling broader ecosystem participation.
- Cross Application Composability
Identity attestations are not limited to a single platform. Multiple protocols can query and reuse them, gradually forming a unified trust network.
In addition, Sign’s architecture supports a wide range of use cases, including onchain social networks, DAO governance, airdrop distribution, and credit evaluation systems.
This level of composability is one of the defining characteristics of Web3 infrastructure.
Future Expansion and Optimization of Sign Technology
As the Web3 ecosystem continues to evolve, several potential directions for expanding Sign Protocol’s technical architecture are emerging.
AI Agent Identity Systems
As AI agents increasingly participate in onchain economies, they will also require identity verification and behavioral tracking systems. Sign’s attestation framework could provide AI agents with behavioral histories, reputation evaluation mechanisms, and proof of task execution.
Onchain Credit Systems
By accumulating historical attestation data over time, it may become possible to build Web3 style credit scoring systems based on verifiable onchain activity.
In addition, Sign may continue improving its architecture in areas such as:
-
More efficient cross chain verification mechanisms
-
Lower cost data storage solutions
-
Stronger privacy preserving computation
These developments could significantly improve the scalability of decentralized identity systems.
Conclusion
Through its onchain attestation model and decentralized identity framework, Sign Protocol introduces a new approach to identity management within the Web3 ecosystem. Users can record identity credentials, behavioral history, and contributions through verifiable credentials, gradually transforming blockchain addresses into trust enabled digital identities.
From a technical perspective, Sign combines attestation schemas, signature verification, cross chain data interaction, and privacy protection mechanisms to support a complete lifecycle of identity generation, verification, and sharing. This architecture improves the security of identity systems while allowing identity data to function across applications and across blockchains.
As new applications such as DAOs, DeFi platforms, onchain social networks, and AI agents continue to emerge, the importance of verifiable identity frameworks will only grow. Infrastructure protocols like Sign are helping Web3 evolve from simple address based systems toward a more comprehensive onchain trust network.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


