TanStack npm supply chain attacked by Mini Shai-Hulud, version 84 injected with credentials to steal code

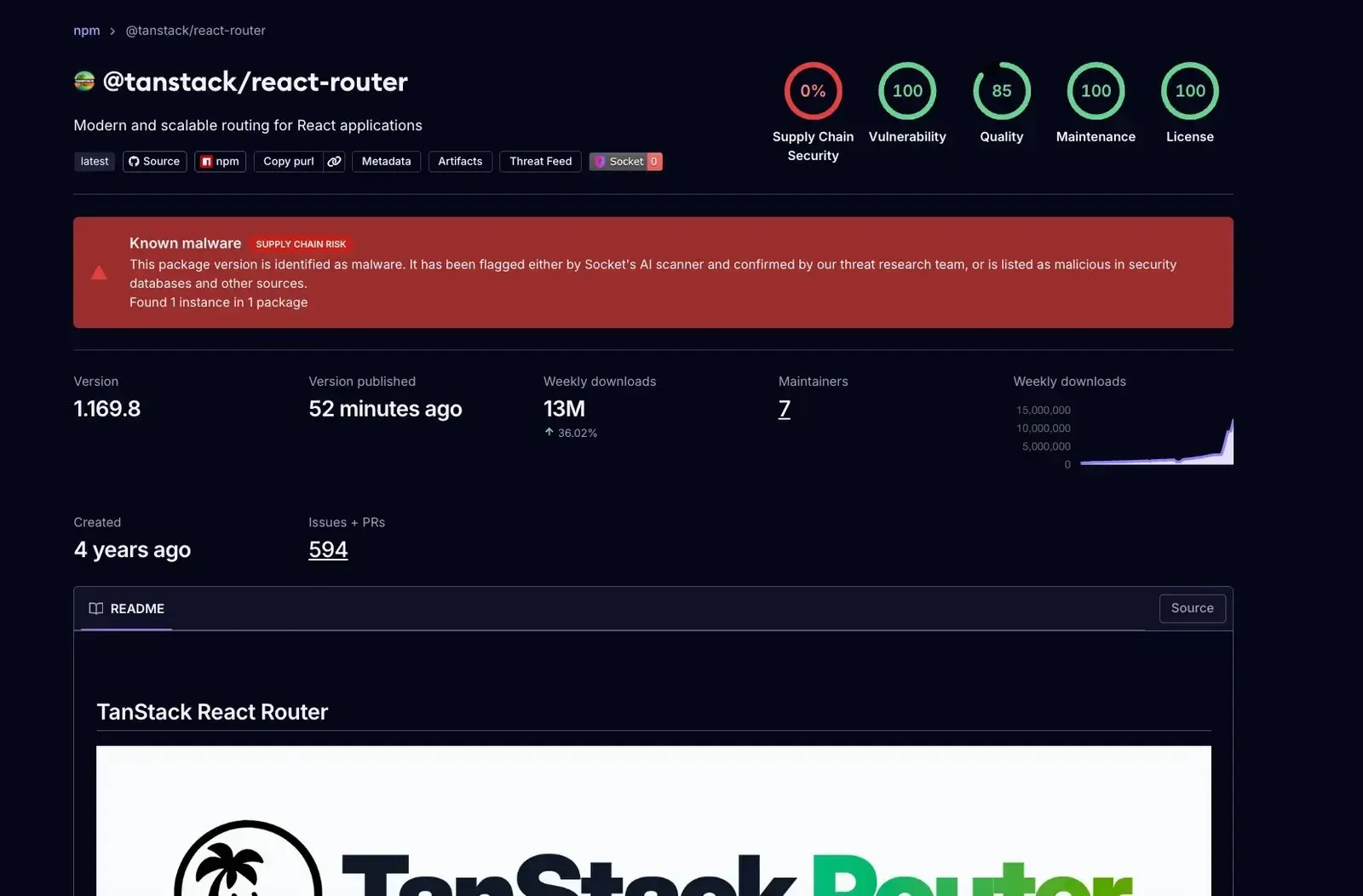
According to a report by Step Security on May 11, the threat group TeamPCP launched a new round of supply-chain worm attacks named “Mini Shai-Hulud,” compromising 84 versions of TanStack npm packages and implanting malicious code, targeting the theft of CI/CD environment credentials. Socket Security marked all malicious versions within six minutes of the release.
Attack Method and Propagation Mechanism
 (Source: Socket Security)
(Source: Socket Security)
According to Step Security’s analysis, the attack used a three-stage process: on May 10, 2026, the attackers created a TanStack/router branch using the GitHub account voicproducoes (ID: 269549300, created on March 19, 2026), and injected a malicious payload; then injected the payload into already-published npm compressed packages; finally, using the hijacked OIDC token, it published through the GitHub Actions release pipeline of the TanStack project itself, releasing malicious versions with SLSA Build Level 3 certification.
According to Step Security’s report, Mini Shai-Hulud is a true self-propagating worm: after stealing credentials from a CI/CD pipeline, it automatically enumerates all packages controlled by the same maintainer and sequentially publishes infected versions. Step Security’s report states this is the first recorded malicious npm worm capable of generating valid SLSA certification.
Core Capabilities of the Malicious Code
According to Step Security and Socket Security’s analysis, the 2.3 MB obfuscated payload (SHA-256: ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c) embedded in the infected packages has the following core capabilities:
Memory scraping: Directly reads the GitHub Actions Runner.Worker process memory via /proc/{pid}/mem to extract all keys, including masked keys
Credential document collection: Collects credentials from more than 100 hardcoded paths, covering AWS / Azure / GCP cloud credentials, SSH keys, npm tokens, cryptocurrency wallets (Bitcoin, Ethereum, Monero, Zcash, Exodus, Electrum, etc.), AI tool configurations (Claude, Kiro), and instant messaging application data
Persistence: Installs persistence hooks at the Claude Code, VS Code, and operating system levels (macOS LaunchAgent / Linux systemd service), remaining effective after reboot
Data exfiltration: Exfiltrates encrypted data through a dual-channel approach—Session Protocol CDN (filev2.getsession.org) and GitHub GraphQL API dead dropboxes (submitting disguised as claude@users.noreply.github.com)
Ransom threats: Embeds the string “IfYouRevokeThisTokenItWillWipeTheComputerOfTheOwner” in the description of newly created npm tokens; revoking the tokens triggers a destructive wipe routine
Main Intrusion Indicators (IOCs)
According to Step Security’s report, the main intrusion indicators for this attack are as follows:
Malicious payload hash value (SHA-256):router_init.js = ab4fcadaec49c03278063dd269ea5eef82d24f2124a8e15d7b90f2fa8601266c
C2 network domains:api.masscan.cloud、filev2.getsession.org、git-tanstack.com、seed1.getsession.org
Attacker GitHub account:voicproducoes (ID: 269549300, email voicproducoes@gmail.com)
Malicious commit:79ac49eedf774dd4b0cfa308722bc463cfe5885c (TanStack/router branch)
The main affected package versions include @tanstack/react-router (1.169.5, 1.169.8), @tanstack/router-core (1.169.5, 1.169.8), and more than 40 TanStack package versions, as well as related packages from organizations such as UiPath, DraftLab, etc.; the full list is continuously updated by Step Security.
Emergency Response Recommendations
According to Step Security’s report, if affected versions are already installed, Step Security recommends:
Immediately clean the affected versions from the lock files and reinstall clean versions; rotate all credentials accessible in CI/CD environments (GitHub tokens, npm tokens, cloud API keys); remove persistence files (.claude/router_runtime.js, .vscode/setup.mjs, etc.); and if the device has cryptocurrency wallet files, immediately transfer funds to new wallet addresses. Step Security specifically warns: before isolating and mirroring the affected devices for forensic analysis, do not revoke npm tokens containing the ransom-threat string.
FAQ
When and by whom was the Mini Shai-Hulud worm discovered?
According to Step Security’s May 11, 2026 report, the attack was detected by an analyst from the StepSecurity AI suite and initiated by the threat group TeamPCP. Socket Security issued a warning on May 12, 2026 on the X platform, stating that all malicious versions had been marked within six minutes after publication.
What technical innovations does this supply-chain attack have?
According to Step Security’s report, Mini Shai-Hulud is the first recorded npm worm that can hijack OIDC tokens and leverage a legitimate Sigstore protocol stack to generate valid SLSA Build Level 3 certification for malicious packages, making the infected versions appear legitimate during standard supply-chain security checks.
How can cryptocurrency wallet users confirm whether they are affected?
According to Step Security’s report, the malicious code targets desktop wallets including Bitcoin (/.bitcoin/wallet.dat), Ethereum (/.ethereum/keystore/*), Monero, Zcash, and Exodus and Electrum. If the device has installed affected versions, Step Security recommends immediately transferring the relevant cryptocurrency wallet funds to new wallet addresses.
Related Articles
A Telegram username sold for a million-dollar price triggers a forged USDT phishing attack
Telegram Usernames Sell for Record $2.1 Million in TON, Followed by Phishing Attacks
Aave and Kelp Complete First Step of rsETH Recovery, Destroy 117,132 rsETH on Arbitrum
Bitcoin Network Flooded With 200,000 Fake Node Addresses Since April 9, Sparking Sybil Attack Concerns
The U.S. DOJ charges three men from Tennessee for cross-state wrench attacks: robbed a California crypto holder of $6.5 million