DeFi Security Incidents on the Rise: A 2026 Practical Guide to Wallet and Authorization Risk Management for Everyday Users
Annual Security Incident Review: Attack Surfaces Are Shifting from "Code Vulnerabilities" to "Permissions and Infrastructure"
Since 2026, public security incidents have shown that risks are no longer confined to isolated smart contract bugs. Instead, threats now emerge concurrently across protocol logic, oracles, frontend gateways, cross-chain verification, and user approvals.
Take the widely discussed Drift incident this year: the market’s attention has focused not only on the scale of losses, but even more on the fragility of governance permissions and oracle connectivity under extreme conditions.
Cases like Rhea Finance have exposed the real and present danger of liquidity pools and pricing mechanisms being manipulated, while the CoW Swap frontend breach serves as a stark reminder that even with robust underlying contracts, a compromised entry point can still result in substantial losses.
In summary, this year’s security events collectively signal a shift: attackers are relying less on brute-forcing code and more on exploiting permission settings, entry points, and user signature habits to move assets. For retail investors, risk management should evolve from simply checking project audits to a four-pronged approach: audit + approval + entry point + emergency response.
Key Lessons from Major Incidents Since 2026
This year’s public cases highlight at least four risk categories that retail investors should take seriously:
-
Protocol and oracle risks: Several DeFi protocols have reported exploits in liquidity pools or oracles, underscoring that “price sources and parameter boundaries” remain high-risk zones.
-
Frontend and domain risks: CoW Swap, for example, disclosed frontend/website security incidents—these attacks often target user entry points first, rather than contracts.
-
Cross-chain verification and message validation risks: In cross-chain scenarios, any gap in the validation path can lead to exponentially greater consequences.
-
Large-scale approval phishing: This year, “approval phishing” has become a major target for law enforcement, with public reports showing victims across multiple countries—clear evidence of industrialized attacks.
The direct takeaway for users: the most common risk isn’t “hackers cracking your Private Key,” but rather “users themselves granting executable permissions to attackers.”
The True High-Risk Factor: Not User Error, But Loss of Permission Control
In most real-world losses, the root cause isn’t complex technical vulnerabilities, but rather these everyday mistakes:
-
Using a single wallet for “asset storage + high-frequency transactions + airdrop testing” over the long term.
-
Retaining Unlimited Approval for unfamiliar contracts.
-
Mistaking “disconnecting from a website” for “revoking approval.”
-
Confirming signatures without understanding their content.
-
Clicking on “official event links” directly from social media.
While hardware wallets are essential, they cannot replace proper approval management. Many thefts don’t require stealing a Private Key—one high-permission approval signature is all it takes.
Wallet Risk Control Framework: Layering First, Then Minimizing Approvals
Treat wallets as an “account system,” not just a single address.
At minimum, divide wallets into three tiers:
-
Cold Wallet (no interaction): For long-term asset storage; only used for deposits and withdrawals, never connected to unknown DApps.
-
Trading Wallet (medium risk): For mainstream protocols and routine trading; set strict asset limits.
-
Experimental Wallet (high risk): For airdrops, new protocol tests, or unknown link interactions; enforce strict amount caps.
Add two hard rules:
-
Set a fixed risk budget per wallet, e.g., “Experimental Wallet should not exceed 2%–5% of Total Assets.”
-
For any new protocol, always start with small test transactions—never grant full approval up front.
The intent of this layered approach: even if something goes wrong, losses remain within a controllable range.
Approval Risk Control Framework: Move from “Click to Confirm” to “Permission Awareness”
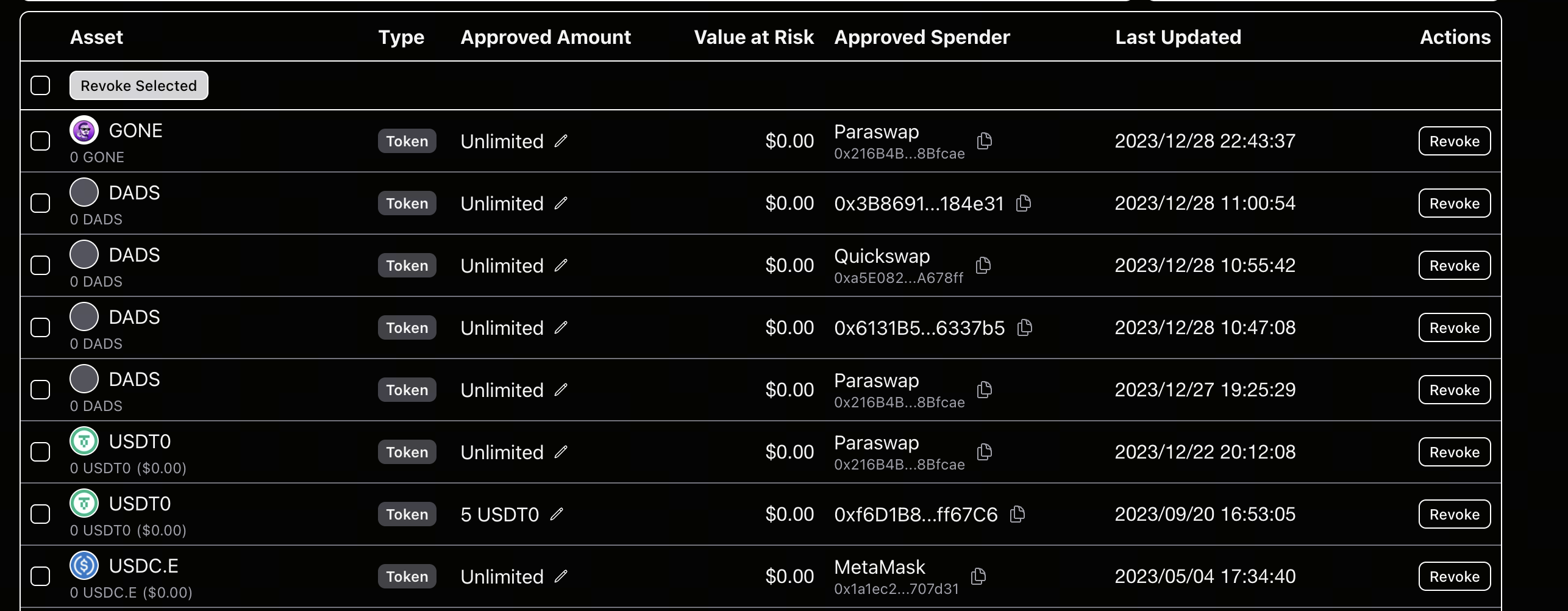
Image source: Revoke.cash page
What most users lack isn’t tools, but a clear process. Here’s a practical “pre-, mid-, and post-approval” workflow:
Before Approval (Pre-Check)
-
Only access via the official main domain—never through comment sections or private message links.
-
Check if the page requests abnormal permissions, such as “Unlimited Approval” or “emergency signature.”
-
For new protocols, review audit reports and community feedback before granting approval.
During Approval (Sign-Check)
-
Verify that the approval address matches the official source.
-
Always prefer limited approvals—never default to Unlimited.
-
Be alert to signatures like
Permit,SetApprovalForAll, andincreaseAllowance. -
If you don’t understand the signature content, cancel—never “blind sign.”
After Approval (Post-Check)
-
Regularly review your approval list—at least once a week.
-
Immediately revoke approvals for unused protocols.
-
After high-risk interactions, review again within 24 hours.
Recommended tools:
A Practical Daily Security Checklist
Follow this actionable checklist:
-
Device: Keep systems and browsers up to date; disable unknown plugins.
-
Network: Avoid conducting high-value signature operations on public Wi-Fi.
-
Account: Enable 2FA for all exchange and Email accounts; never reuse passwords.
-
Wallet: Use layered wallets and enforce risk limits.
-
Approval: Clean up unused approvals weekly; conduct a full review monthly.
-
Behavior: Treat any “urgent signature” or “limited-time claim” as a high-alert scenario by default.
For high-frequency users, add two more steps:
-
Maintain a whitelist of official contract addresses for commonly used protocols.
-
For large transfers, add a “second confirmation delay” to prevent impulsive mistakes.
24-Hour Emergency SOP for Theft or Mis-Approval
If you suspect an issue, don’t blame yourself—immediately follow this protocol:
-
Stop all interactions: disconnect from websites and pause all new signatures.
-
Quickly transfer unaffected assets to a Cold Wallet or new address.
-
Revoke critical approvals: prioritize revoking high-permission approvals for high-value Tokens.
-
Investigate entry points: review recent links, browser plugins, and device anomalies.
-
Preserve evidence: save Transaction Hashes, suspicious addresses, and screenshots of signature records.
-
Coordinate externally: contact project security teams, Wallet providers, and on-chain security organizations.
If losses have already occurred, shift your goal from “recovering everything” to “preventing further losses.” In many cases, secondary losses far exceed the initial incident.
Conclusion: Security Is an Ongoing Process, Not a One-Time Setting
During periods of heightened DeFi security incidents, users shouldn’t focus on “fear,” but on building robust processes.
You don’t need to become a security engineer, but you should make these steps second nature:
-
Wallet layering
-
Minimal approval
-
Regular revocation
-
Decoding before signing
-
Having an SOP for incidents
On-chain, permissions are assets. How you manage those permissions determines whether you’ll stay in the game for the long run.
Related Articles

In-depth Explanation of Yala: Building a Modular DeFi Yield Aggregator with $YU Stablecoin as a Medium

Sui: How are users leveraging its speed, security, & scalability?
Dive into Hyperliquid
What Is a Yield Aggregator?

What is Stablecoin?


