Elliptic Links $286 Million Drift Protocol Exploit to North Korean Hackers
 Blockchain analytics firm Elliptic reported on April 2, 2026 that the $286 million exploit of Solana-based Drift Protocol carries multiple indicators of involvement by North Korea’s state-sponsored DPRK hacker group, marking what would be the eighteenth such attack tracked by Elliptic this year.
Blockchain analytics firm Elliptic reported on April 2, 2026 that the $286 million exploit of Solana-based Drift Protocol carries multiple indicators of involvement by North Korea’s state-sponsored DPRK hacker group, marking what would be the eighteenth such attack tracked by Elliptic this year.
The April 1 exploit, the largest DeFi hack of 2026 to date, collapsed Drift’s total value locked from approximately $550 million to under $250 million, with on-chain behavior, laundering methodologies, and network-level signals mirroring prior state-linked operations.
Elliptic Identifies Premeditated On-Chain Behavior and Cross-Chain Laundering Patterns
Elliptic’s analysis points to activity that appears “premeditated and carefully staged,” with early test transactions and pre-positioned wallets preceding the main event. The attacker’s wallet was created approximately eight days before the exploit and received a small test transfer from a Drift vault during that period, suggesting advance planning.
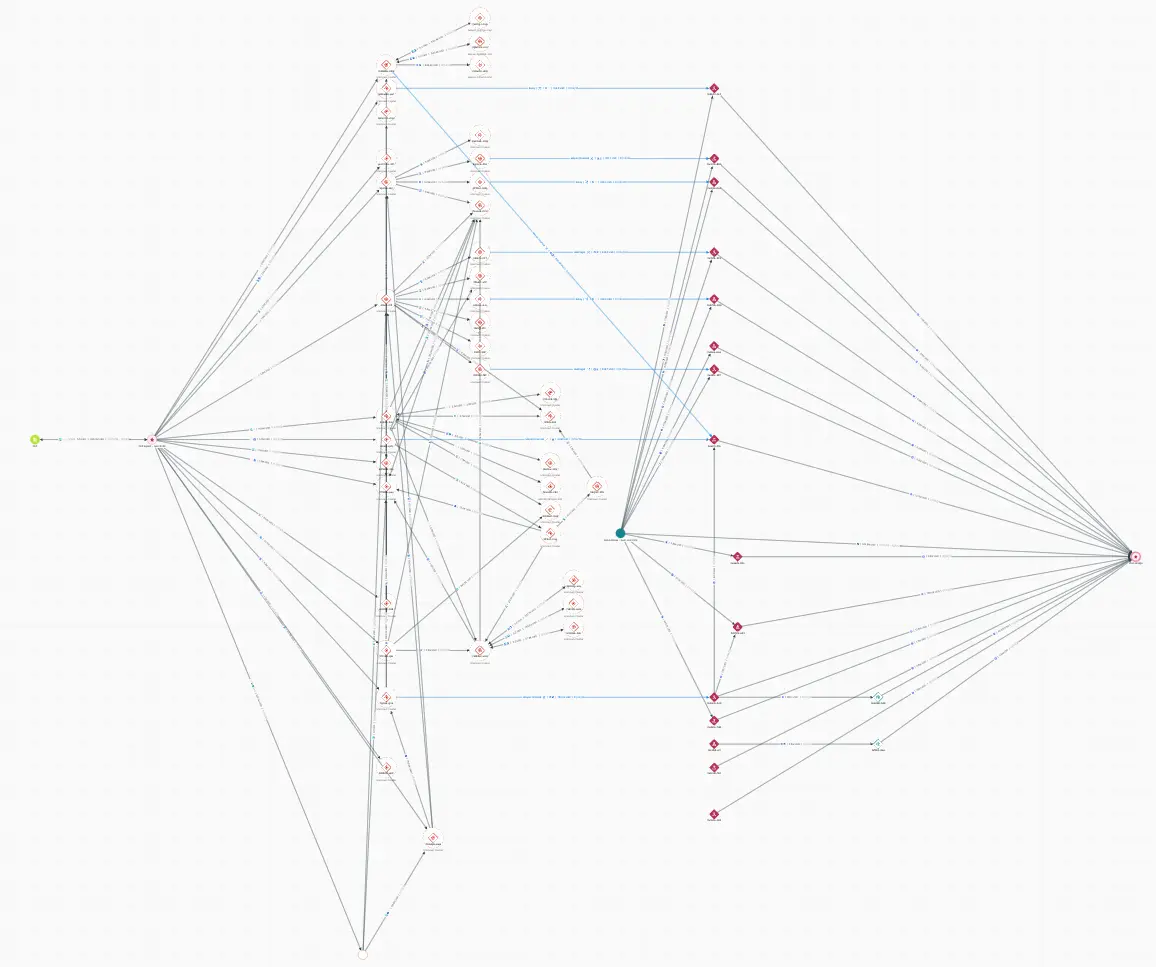 (Source: Elliptic Investigator)
(Source: Elliptic Investigator)
Once executed, funds were rapidly consolidated and swapped, bridged across chains, and converted into more liquid assets, reflecting a structured, repeatable laundering flow designed to obscure origin while maintaining control. The attacker drained three core vaults: the JLP Delta Neutral, SOL Super Staking, and BTC Super Staking vaults. The largest single transfer involved approximately 41.7 million JLP tokens, valued at roughly $155 million at the time of the theft. Additional assets stolen included USDC, SOL, cbBTC, wBTC, and liquid staking tokens.
Within an hour of the attack beginning, the attacker systematically drained the vast majority of Drift’s liquidity by withdrawing assets from multiple protocol vaults. According to blockchain security firm PeckShield, the preliminary cause appears to be a compromise of the protocol’s administrator private keys, which gave the attacker privileged access to initiate withdrawals and alter administrative controls.
Solana Account Model Complicates Investigation of Multi-Asset Exploit
Elliptic notes that Solana’s account model presents a central challenge for investigators. Because each asset is held in a separate token account, activity tied to a single actor can appear fragmented across multiple addresses. The attacker drained more than 15 types of tokens across multiple vaults, meaning the attacker’s JLP, USDC, SOL, cbBTC, and other stolen assets each sit in distinct on-chain addresses.
Analytics providers that treat these addresses as unrelated will see fragments of the attacker’s activity, not the complete picture. Elliptic’s clustering approach connects token accounts back to a single entity, allowing exposure to be identified regardless of which address is screened. The case also emphasizes how laundering has become inherently cross-chain, with funds moving from Solana to Ethereum and beyond, requiring holistic cross-chain tracing capabilities.
DPRK-Linked Crypto Theft Escalates as Elliptic Tracks $300 Million Stolen in 2026
If confirmed, this incident would represent the eighteenth DPRK-linked act Elliptic has tracked in 2026, with over $300 million stolen so far. DPRK-linked actors are believed to have stolen over $6.5 billion in cryptoassets in recent years. The US government has linked the thefts to the funding of North Korea’s weapons of mass destruction program.
In December 2025, a Chainalysis report revealed DPRK hackers stole a record $2 billion of crypto in 2025, including the $1.4 billion Bybit breach, representing a 51% increase from the previous year. The US Treasury Department last month reiterated that North Korea uses stolen assets to fund its weapons program.
The Drift exploit also takes place amid a broader escalation of DPRK-linked activity targeting the crypto ecosystem, including a recent supply chain compromise of the axios npm package, which Google attributed to DPRK threat actor UNC1069.
Drift Protocol confirmed the exploit on X, stating it was experiencing an “active attack” and that deposits and withdrawals had been suspended. The team is coordinating with multiple security firms, cross-chain bridges, and exchanges to contain the incident. Drift’s token has dropped over 40% to roughly $0.06 since the hack.
FAQ
How much was stolen in the Drift Protocol exploit and who is suspected?
Approximately $286 million was stolen from Drift Protocol on April 1, 2026. Elliptic has identified multiple indicators suggesting involvement by North Korea’s state-sponsored DPRK hacker group, including premeditated on-chain behavior and laundering patterns consistent with prior state-linked operations.
What made the Drift exploit particularly difficult to trace?
The attacker drained more than 15 types of tokens across multiple vaults. Solana’s account model creates separate token accounts for each asset type held by a single entity, meaning the attacker’s various stolen assets each sit in distinct on-chain addresses. Without clustering these addresses, investigators see fragments rather than the complete picture of the attack.
How does this incident fit into broader DPRK hacking trends?
If confirmed, this would be the eighteenth DPRK-linked act Elliptic has tracked in 2026, with over $300 million stolen so far. DPRK-linked actors are believed to have stolen over $6.5 billion in cryptoassets in recent years, with the US government linking these thefts to funding the country’s weapons of mass destruction program.