#LayerZeroCEOAdmitsProtocolFlaws
LayerZero CEO Confession: Protocol Vulnerabilities and After $290M Hack
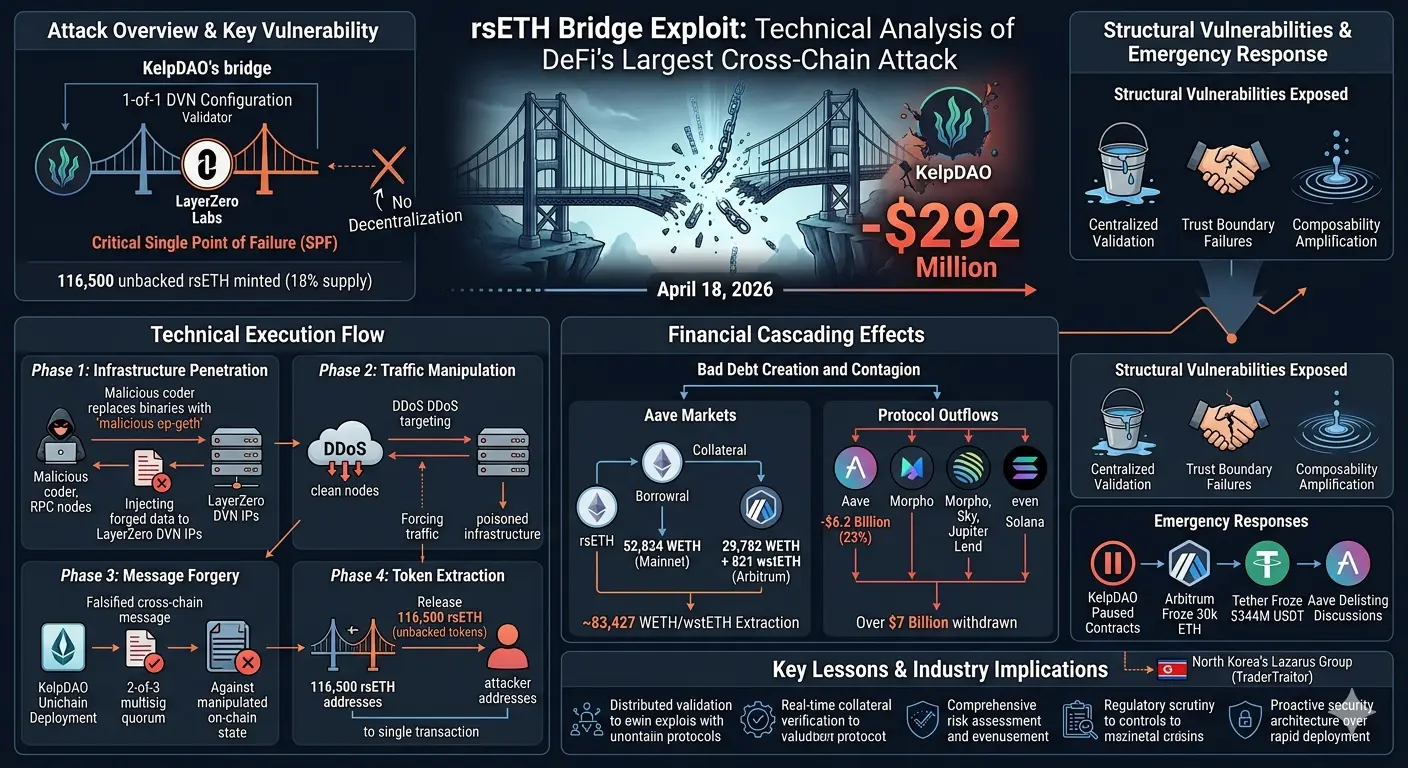
The cross-chain world was shaken in April-May 2026. LayerZero CEO Bryan Pellegrino revealed a critical flaw in the Across Protocol token contract. The same week, the $292 million KelpDAO hack occurred. The community rose up: “Just increasing the number of validators isn’t enough.”
1. CEO Confession: “Red Alert” in Token Contract
Pellegrino addressed the Across team: “You accidentally left a function that should be private in your ERC20 implementation public. The contract owner can withdraw tokens from any wallet and set the balance to zero. Also, Across and UMA contracts have unlimited minting rights.”
Suggested solution: Transfer contract ownership to an immutable smart contract. Disable mint/burn rights. Because this is a permanent vulnerability. Pellegrino: “If there’s a bug bounty, contact the LayerZero team.”
2. $292M KelpDAO Disaster: Responsibility Dispute
Around April 20, KelpDAO’s LayerZero bridge was drained: 116,500 rsETH, $292M stolen. Lazarus Group suspected.
LayerZero: “The attack was not on our protocol, but an infrastructure attack. KelpDAO used a 1-of-1 DVN, so it’s an isolated incident.” In other words, they trusted a single validator network; our recommendation was multi-DVN.
The community is angry: “Your RPC infrastructure was hacked, you can’t just blame KelpDAO.” 47% of OApp still uses 1-of-1 DVN. At risk is $4.5 billion.
3. Structural Issue: DVN Architecture
LayerZero claims “modular security”: Applications choose their own DVNs. But if default settings are weak, projects unknowingly entrust a single validator. This happened with KelpDAO too. Attackers poisoned RPCs and approved fake messages.
Stani Kulechov warned: “Bridge exploits are an existential threat to DeFi. After Ronin, Poly Network, Nomad, now LayerZero-based bridges are in the spotlight.”
Market Impact • ZRO Token: Fell 20% after the hack, ranging from $1.47 to $2.28. Despite a 5.18% jump in the last 3 days, the trend remains downward. • TVL Risk: $4.5B+ OApp operates with 1-of-1 DVN. If similar attacks recur, contagion risk is high. • Trust Crisis: “Zero contagion” was claimed, but the community is not convinced. Bridge security is now the top priority in DeFi.
Summary: LayerZero says “applications choose their own security,” but defaults put billions at risk. The CEO’s disclosure about Across was well-intentioned, but the “responsibility is not ours” stance after KelpDAO drew criticism. Protocol-level security cannot be solved simply by adding more validators. Industry-wide audits, standards, and transparency are essential.
#GateSquareMayTradingShare
#GateSquareMayTradingShare
#LayerZeroCEOAdmitsProtocolFlaws
LayerZero CEO Confession: Protocol Vulnerabilities and After $290M Hack
The cross-chain world was shaken in April-May 2026. LayerZero CEO Bryan Pellegrino revealed a critical flaw in the Across Protocol token contract. The same week, the $292 million KelpDAO hack occurred. The community rose up: “Just increasing the number of validators isn’t enough.”
1. CEO Confession: “Red Alert” in Token Contract
Pellegrino addressed the Across team: “You accidentally left a function that should be private in your ERC20 implementation public. The contract owner can withdraw tokens from any wallet and set the balance to zero. Also, Across and UMA contracts have unlimited minting rights.”
Suggested solution: Transfer contract ownership to an immutable smart contract. Disable mint/burn rights. Because this is a permanent vulnerability. Pellegrino: “If there’s a bug bounty, contact the LayerZero team.”
2. $292M KelpDAO Disaster: Responsibility Dispute
Around April 20, KelpDAO’s LayerZero bridge was drained: 116,500 rsETH, $292M stolen. Lazarus Group suspected.
LayerZero: “The attack was not on our protocol, but an infrastructure attack. KelpDAO used a 1-of-1 DVN, so it’s an isolated incident.” In other words, they trusted a single validator network; our recommendation was multi-DVN.
The community is angry: “Your RPC infrastructure was hacked, you can’t just blame KelpDAO.” 47% of OApp still uses 1-of-1 DVN. At risk is $4.5 billion.
3. Structural Issue: DVN Architecture
LayerZero claims “modular security”: Applications choose their own DVNs. But if default settings are weak, projects unknowingly entrust a single validator. This happened with KelpDAO too. Attackers poisoned RPCs and approved fake messages.
Stani Kulechov warned: “Bridge exploits are an existential threat to DeFi. After Ronin, Poly Network, Nomad, now LayerZero-based bridges are in the spotlight.”
Market Impact • ZRO Token: Fell 20% after the hack, ranging from $1.47 to $2.28. Despite a 5.18% jump in the last 3 days, the trend remains downward. • TVL Risk: $4.5B+ OApp operates with 1-of-1 DVN. If similar attacks recur, contagion risk is high. • Trust Crisis: “Zero contagion” was claimed, but the community is not convinced. Bridge security is now the top priority in DeFi.
Summary: LayerZero says “applications choose their own security,” but defaults put billions at risk. The CEO’s disclosure about Across was well-intentioned, but the “responsibility is not ours” stance after KelpDAO drew criticism. Protocol-level security cannot be solved simply by adding more validators. Industry-wide audits, standards, and transparency are essential.
#GateSquareMayTradingShare
#GateSquareMayTradingShare
#LayerZeroCEOAdmitsProtocolFlaws